Okta SSO with openZro Self-Hosted
Okta is a cloud-based identity and access management service for enterprise use, providing single sign-on, multi-factor authentication, and lifecycle management.
Management Setup (Recommended)
Add Okta as an external IdP directly in the openZro Management Dashboard. This is the simplest approach and recommended for most deployments.
Prerequisites
- openZro self-hosted with embedded IdP enabled
- Okta Workforce Identity Cloud account
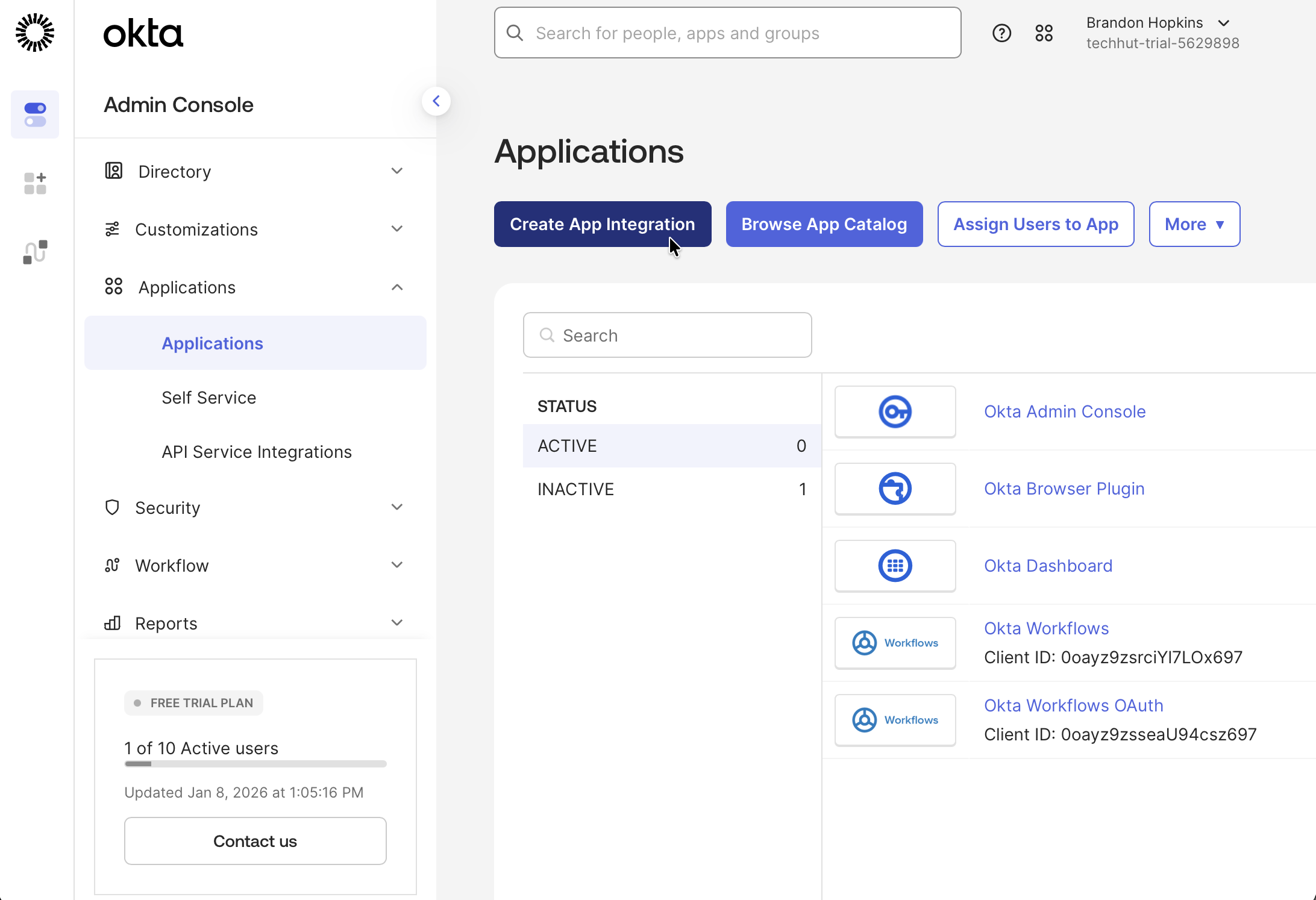
Step 1: Start Creating OIDC Application in Okta
- Navigate to Okta Admin Dashboard
- Click Applications → Applications
- Click Create App Integration
- Select:
- Sign-in method:
OIDC - OpenID Connect - Application type:
Web Application
- Sign-in method:
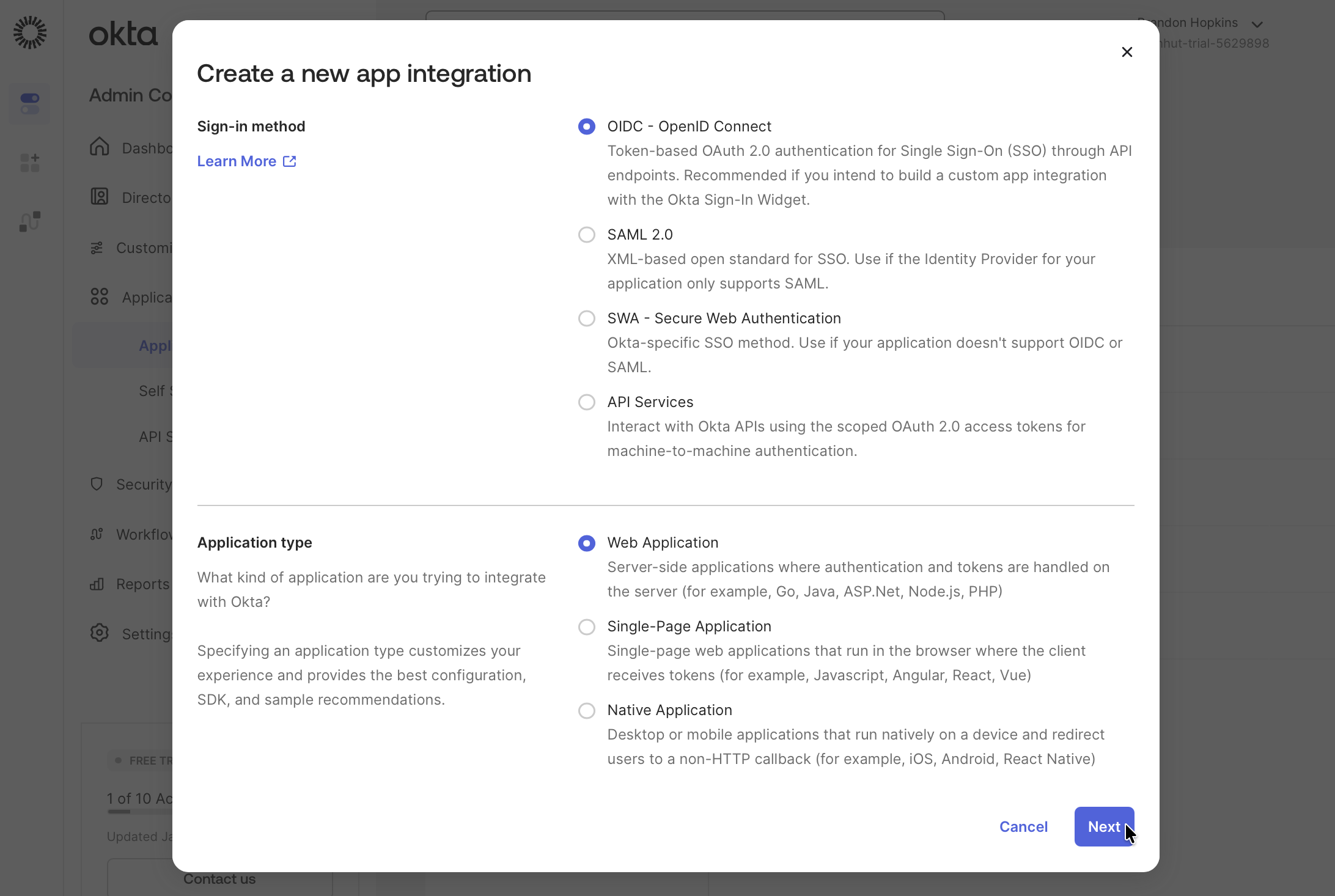
- Click Next
- Fill in:
- App integration name:
openZro - Grant type:
Authorization Code - Leave redirect URIs empty for now (you'll add this in Step 3)
- App integration name:
- Under Assignments, select an option for controlled access:
- Allow everyone in your organization to access (recommended for testing)
- Limit access to selected groups (for production)
- Skip group assignment for now (assign later)
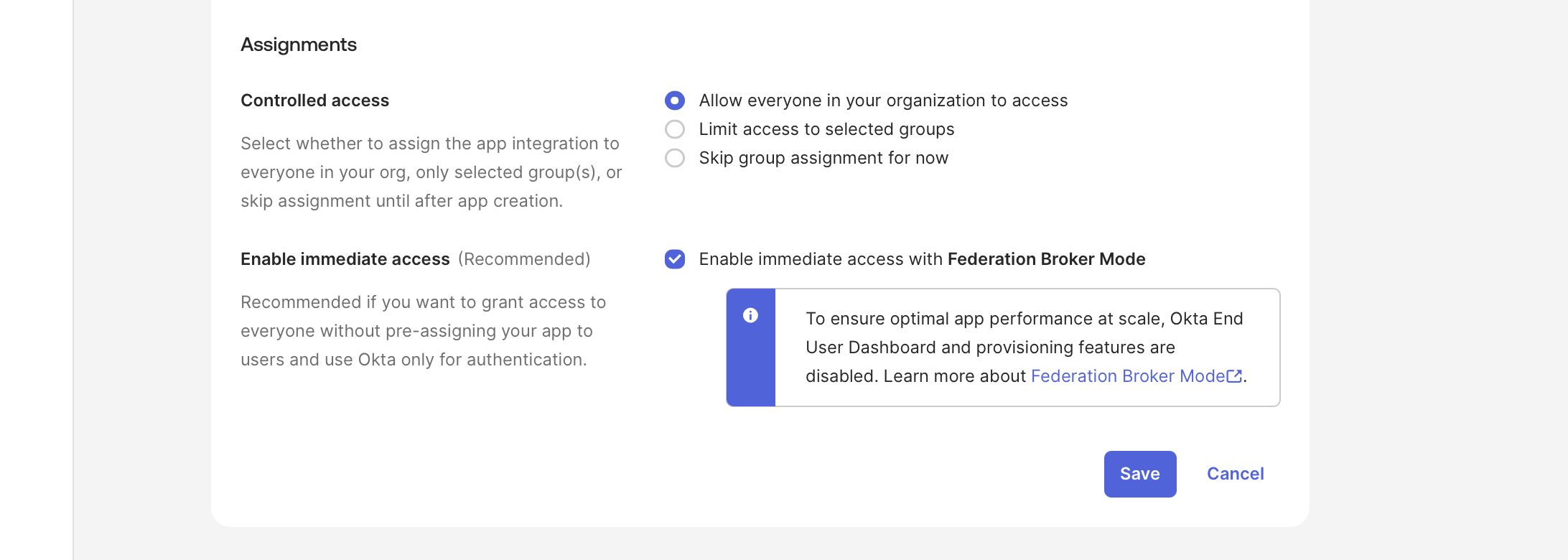
- Don't click Save yet — keep this tab open and proceed to Step 2
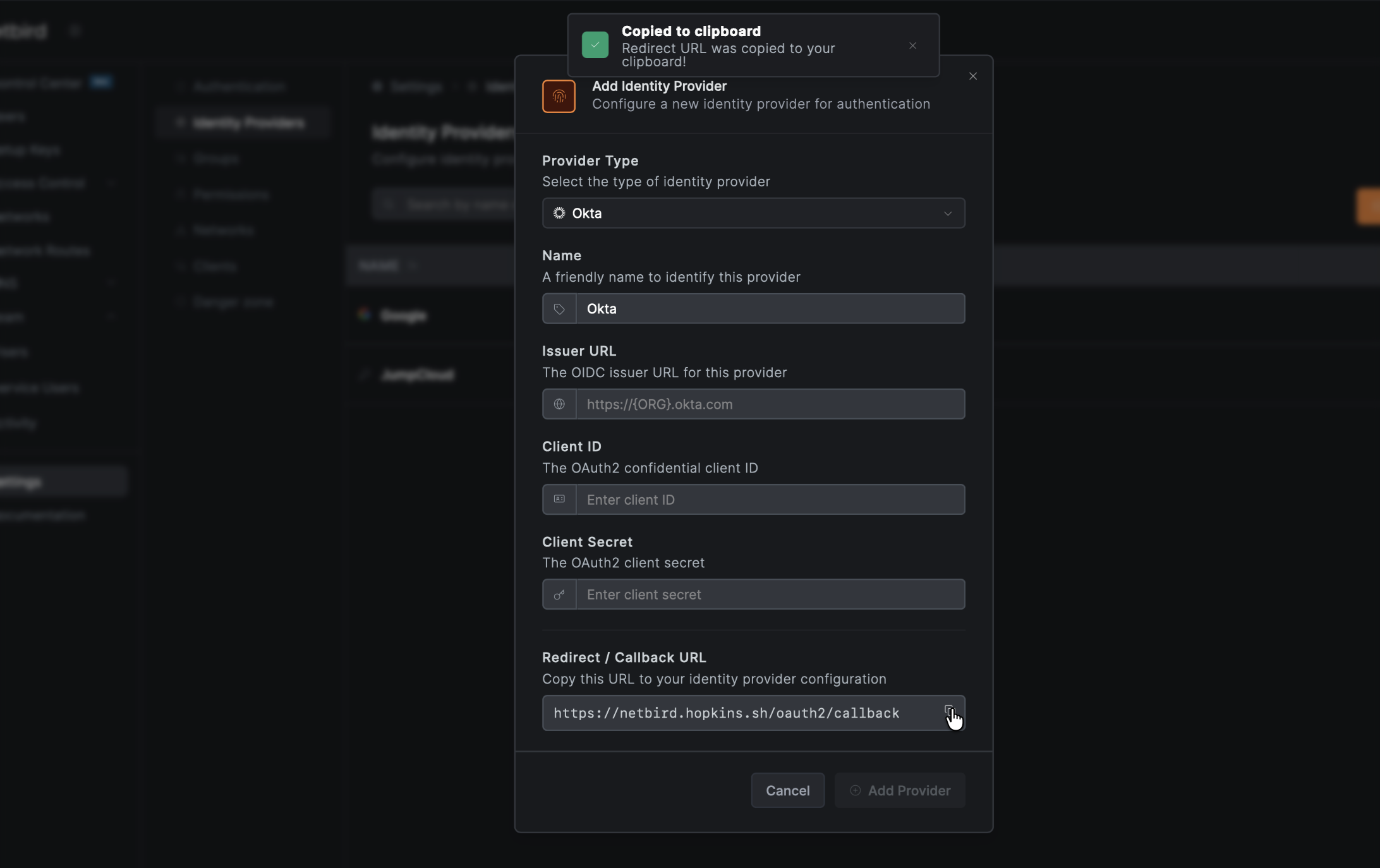
Step 2: Get Redirect URL from openZro
- Open a new tab or window and log in to your openZro Dashboard
- Navigate to Settings → Identity Providers
- Click Add Identity Provider
- Fill in the fields:
| Field | Value |
|---|---|
| Type | Okta |
| Name | Okta (or your preferred display name) |
| Client ID | From Okta application (will fill after Step 3) |
| Client Secret | From Okta application (will fill after Step 3) |
| Issuer | Your Okta URL (e.g., https://your-org.okta.com) |
- Copy the Redirect URL that openZro displays (but don't click Add Provider yet)
Step 3: Complete Okta Application Setup
- Return to the Okta tab
- In the Sign-in redirect URIs field, paste the redirect URL you copied from openZro
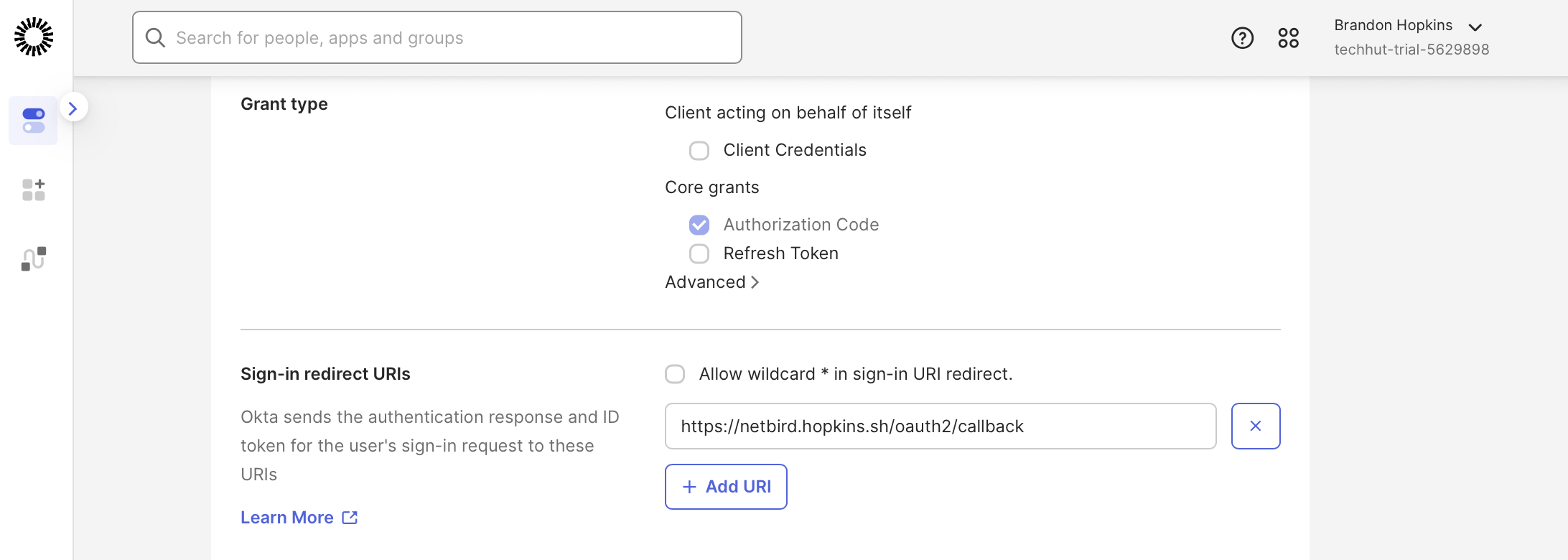
- Click Save
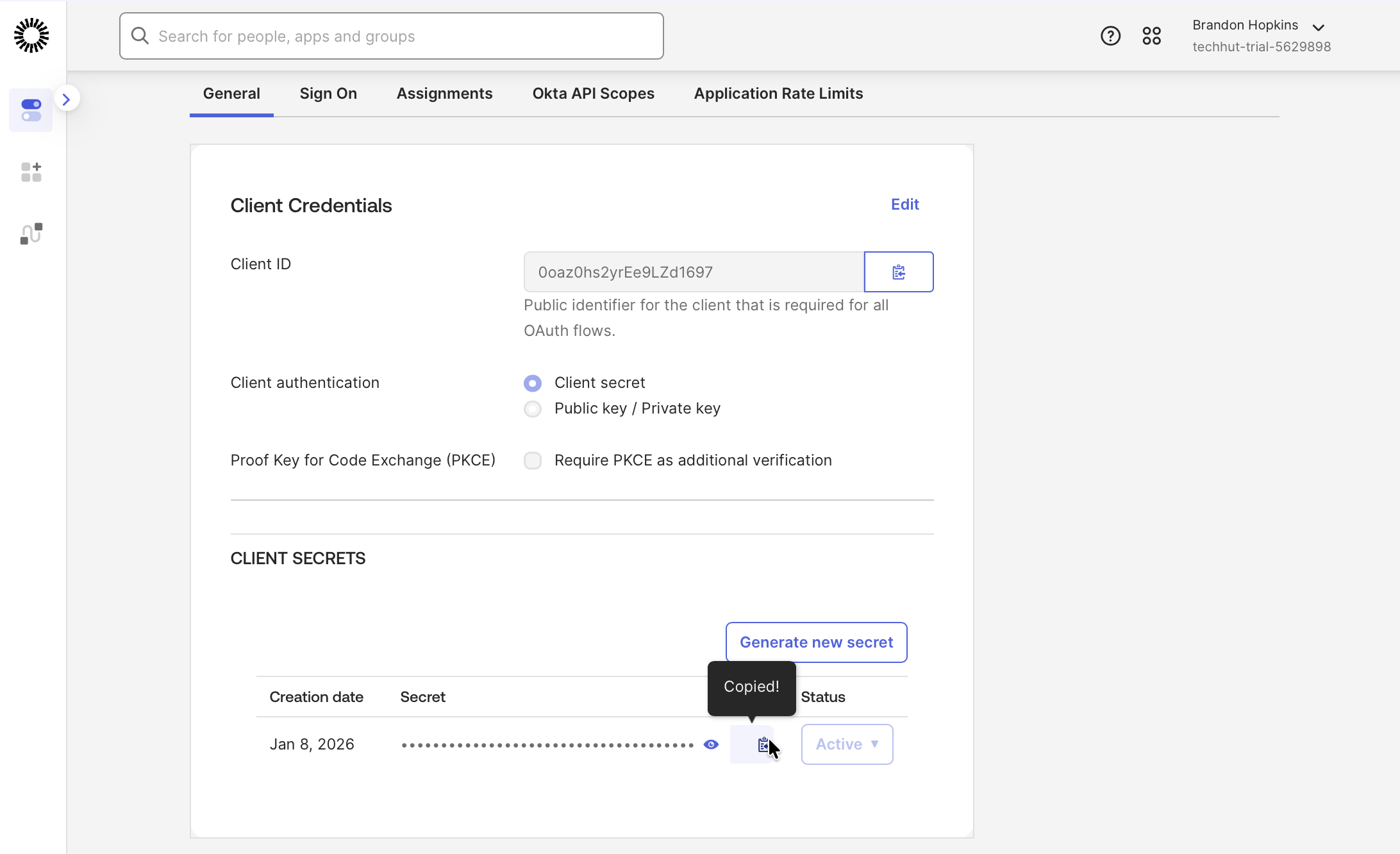
- Note the Client ID and Client Secret — you'll need these for Step 4
Step 4: Complete openZro Setup
- Return to the openZro tab
- Fill in the Client ID and Client Secret from Step 3
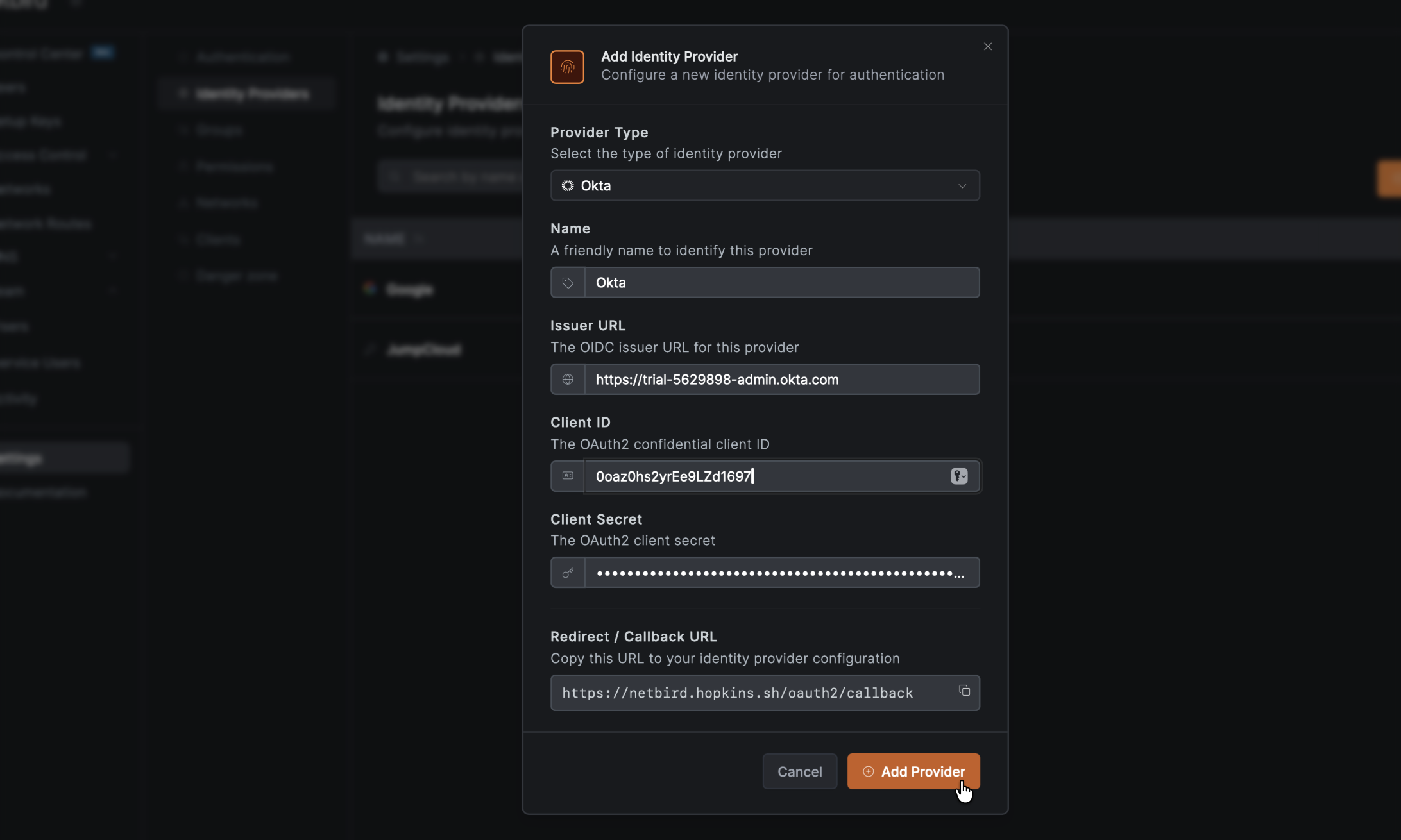
- Click Add Provider
Step 5: Test the Connection
- Log out of openZro Dashboard
- On the login page, you should see an "Okta" button
- Click it and authenticate with your Okta credentials
- You should be redirected back to openZro and logged in. Unless your user approval setting were changed you will need to log back into your local admin account to approve the user.
Configuring JWT 'groups' Claim
To sync Okta groups with openZro, you need to configure Okta to include a groups claim in the ID token. There are two methods depending on your Okta setup.
Method 1: Application-Level Configuration (Recommended)
This method works with Okta's org authorization server and is the simplest approach:
- In Okta Admin Console, go to Applications → Applications
- Select your openZro application
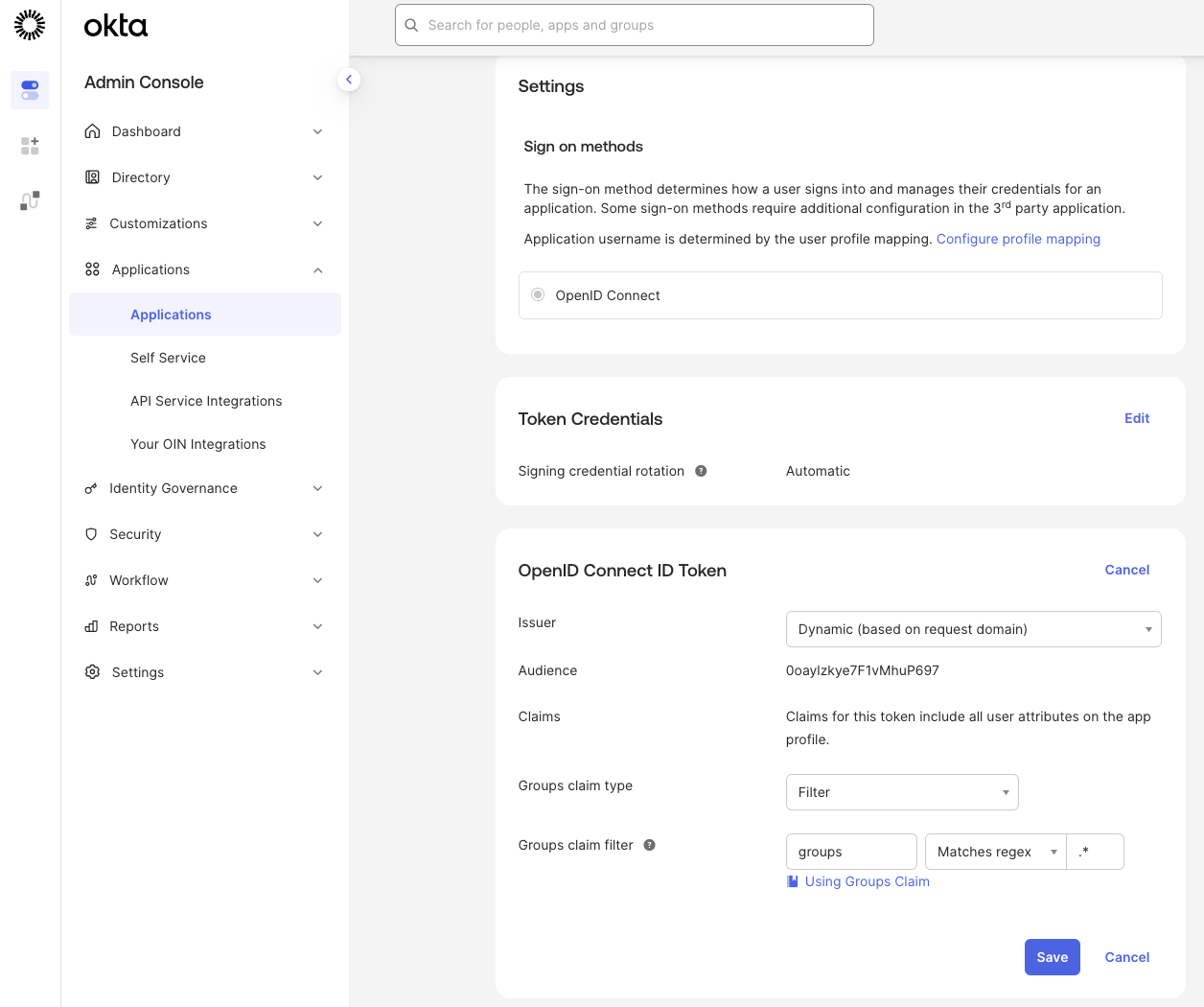
- Go to the Sign On tab
- Click Edit in the OpenID Connect ID Token section
- Under Group claim type, select Filter
- In Group claims filter:
- Claim name:
groups - Filter: Select Matches regex and enter
.*(to include all groups)
- Claim name:
- Click Save
Method 2: Custom Authorization Server
If you're using a custom authorization server (required for access token claims):
- In Okta Admin Console, go to Security → API
- Select your custom authorization server
- Go to the Claims tab
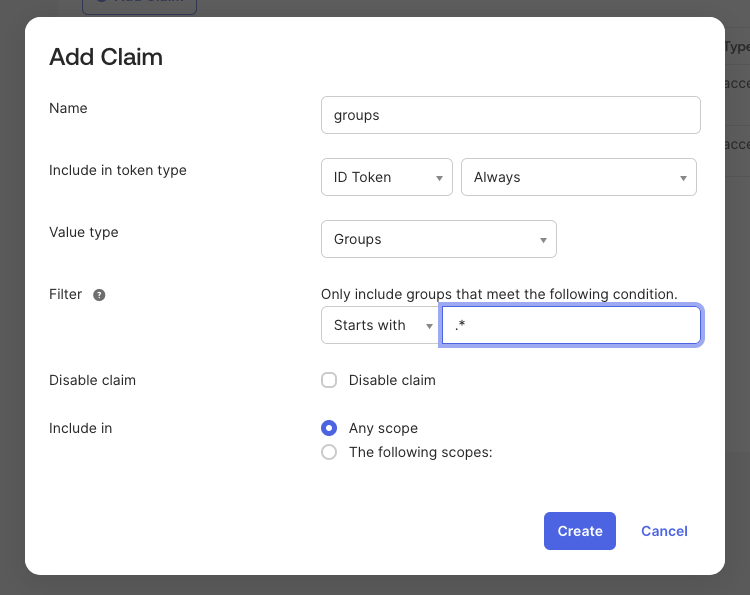
- Click Add Claim
- Configure the claim:
- Name:
groups - Include in token type:
ID Token(select Always) - Value type:
Groups - Filter: Select Matches regex and enter
.*
- Name:
- Click Create
The groups claim has a limit of 100 groups. If a user belongs to more than 100 groups that match the filter, the request will fail. Use a more specific filter (e.g., ^openZro-.*) to limit the groups included.
Enable JWT Group Sync in openZro
After configuring Okta:
- In openZro Dashboard, go to Settings → Groups
- Enable JWT group sync
- Set JWT claim to
groups - Optionally configure JWT allow groups to restrict access
Standalone Setup (Advanced)
Use Okta as your primary identity provider instead of openZro's embedded IdP. This option gives you full control over authentication and user management, is recommended for experienced Okta administrators as it also requires additional setup and ongoing maintenance.
For most deployments, the embedded IdP is the simpler choice — it's built into openZro, fully integrated, and requires minimal configuration to get started. For this implementation, go back up to the Management Setup (Recommended) section above.
For detailed instructions on the standalone setup, see the Okta SSO with openZro Self-Hosted (Legacy) documentation.
If you prefer to have full control over authentication, consider self-hosted alternatives like PocketID.
Troubleshooting
"Invalid redirect URI" error
- Ensure all redirect URIs are configured in Okta
- Check for trailing slashes
- Verify the application type matches the use case
"Invalid issuer" error
- Ensure the issuer is set to use the Okta URL (not dynamic)
- Verify the OIDC configuration endpoint returns valid JSON